SAML: Integrate with Microsoft Azure AD
Related Video:
KACE Cloud subscribers can use Azure Active Directory (Azure AD) when setting up single sign-on (SSO). Configuring SSO to use Azure AD allows users to sign in to KACE Cloud using their managed Azure AD accounts.
To set up an identity provider protocol using SAML and Azure AD, open both KACE Cloud and your Azure Active Directory Server.
- Open both KACE Cloud and your Azure Active Directory Server.
- In KACE Cloud, complete the following steps:
- Select the Settings tab in top navigation.
- In left navigation, under Integrations, choose Single Sign-On (SSO) .
- Select SAML v2.0.

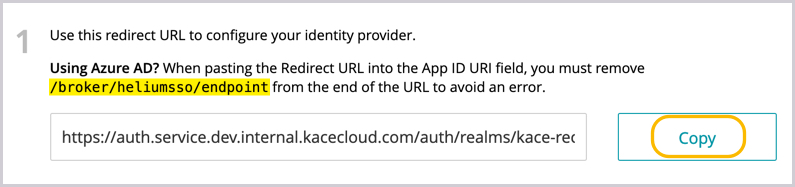
- In KACE Cloud, in the SSO Wizard, copy the redirect URL to configure the identity provider. Save this information for later use.
- In Azure AD, provide the basic SAML configuration details.
- Select Enterprise applications in the left panel of the main directory.
- Click New application to display the Browse Azure AD Gallery list.
- Click Create your own application to create the new KACE Cloud app, then provide the following details:
- What's the name of your app: For example, you can type KACE Cloud.
- Integrate any other application you don't find in the gallery (Non-gallery): Ensure this option is selected.
- Click Create.
The detail pages for the new enterprise application are displayed.
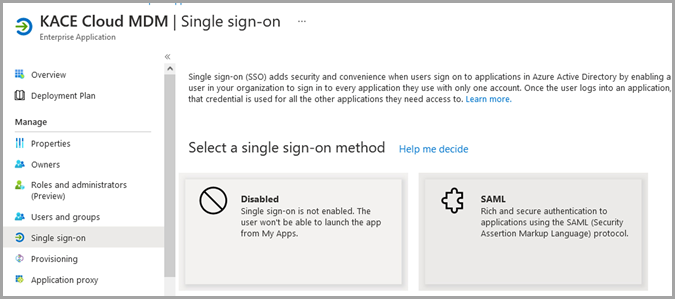
- In the left panel, select Single sign-on.
- In the Select a single sign-on method section of the page, click the SAML button to display the Set up Single Sign-On with SAML page.
- In the top-right corner of the Basic SAML Configuration section, click Edit.
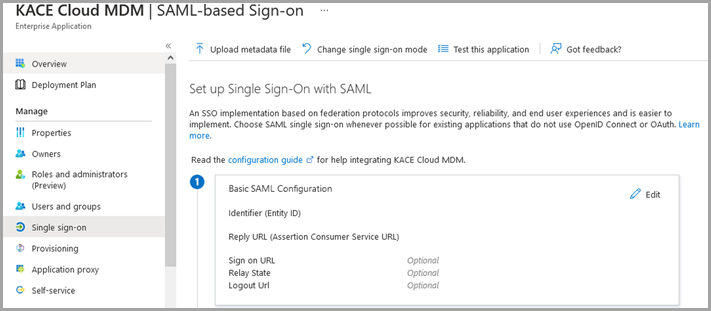
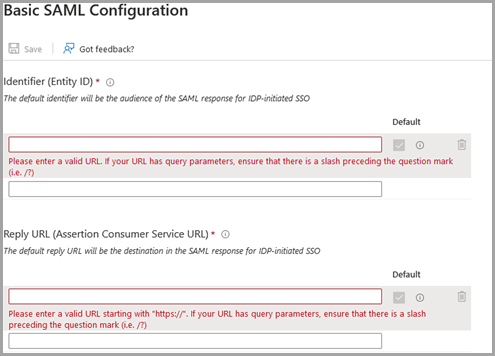
- On the Basic SAML Configuration page that appears, provide the following information:
- Identifier (Entity ID): Type the redirect URL copied from the KACE Cloud Single Sign-On (SSO) page (see step 3), making sure you remove the trailing /broker/heliumsso/endpoint.
- Reply URL (Assertion Consumer Service URL):Type the redirect URL copied from the KACE Cloud Single Sign-On (SSO) page, making sure you include the trailing /broker/heliumsso/endpoint.
- Sign on URL:Provide the URL to the customer's KACE Cloud tenant. It can either be the URL to the customer's administrative or device enrollment portal, such as:
- https://<tenant>.kacecloud.com
- https://<tenant>.enroll.kacecloud.com
- Click Save.
- Import the configuration URL from the identity provider.
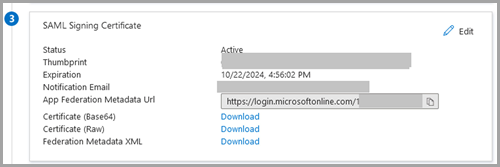
- In Azure AD, on the Azure AD enterprise application SAML-based Sign-on page, in the SAML Signing Certificate section, click the Copy button to the right of the App Federation Metadata Url field.
- In the KACE Cloud, on the Single Sign-On (SSO) page, paste the newly copied App Federation Metadata Url value into the Import from URL field.
- Click Import.
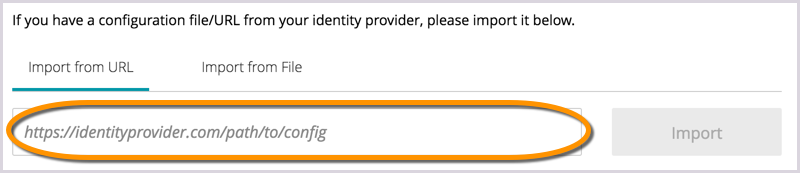
When imported, the majority of information is populated in the main SSO configuration screen of KACE Cloud. The location of the SSO configuration file or URL varies based on identity provider. If you cannot determine where the file or URL is located within your identity provider's application interface, see their documentation.
- In Azure AD, on the Azure AD enterprise application SAML-based Sign-on page, in the SAML Signing Certificate section, click the Copy button to the right of the App Federation Metadata Url field.
- In Azure AD, enable and assign Azure AD users and groups to the KACE Cloud application enterprise application.
You must ensure the Azure AD enterprise application is enabled, and then must also decide whether all Azure AD users are allowed to log in into KACE Cloud, or if only users and groups assigned to the KACE Cloud Azure AD enterprise application are allowed to log in to KACE Cloud.
- Locate and open the KACE Cloud enterprise application in Azure AD that you created in the previous steps, then select Properties.
- Ensure that the Enabled for users to sign-in is set to Yes.
- Set Visible to users to No.
- If you want to limit which Azure AD usersor groups are allowed to login to KACE Cloud, set Assignment required to Yes, otherwise set to No.
- Click Save.
- If you set Assignment required to Yes, select Users and groups in the left navigation menu. Click the Add user/group to assign Azure AD users and groups to this enterprise application.
- In Azure AD, configure the identity provider to send group information by modifying the user attributes and claims of the enterprise application.
If you want to be able to automatically assign a KACE Cloud role to an Azure AD user that logs in using SSO based on the user's group membership in Azure AD, you must configure the Azure AD enterprise application for KACE Cloud to send information for values such as security group and distribution list membership.
- Locate and open the KACE Cloud enterprise application in Azure AD that you created in the previous steps, select Single Sign On configuration, and then in the User Attributes & Claims area, click Edit to display details and settings.
- Click Add a group claim.

- Select the groups that you want to include in the token.


IMPORTANT: In a previous step, if you limited which Azure AD users/groups are allowed to login to KACE Cloud by setting the Assignment required to Yes, select the Groups assigned to the application option, to limit the amount of data included in the user's login token. This helps large organizations to avoid Azure AD truncating the group data from the login token by limiting the reported groups to only those that are assigned to this enterprise application.
- Click Save
-
In KACE Cloud, validate the identity provider signatures.
- Ensure the Validate signatures of identity provider requests/responses check box is selected, then review the contents ot Validating Certificates field.
It is highly recommended to leave the Validate signatures of identity provider requests/responses check box selected to ensure optimal security. Disable this check box only for troubleshooting purposes.
If the certificate value is obtained after importing the App Federation Metadata Url in step 5, it appears in the Validating Certificates field. Otherwise, you must manually copy and paste the appropriate value.
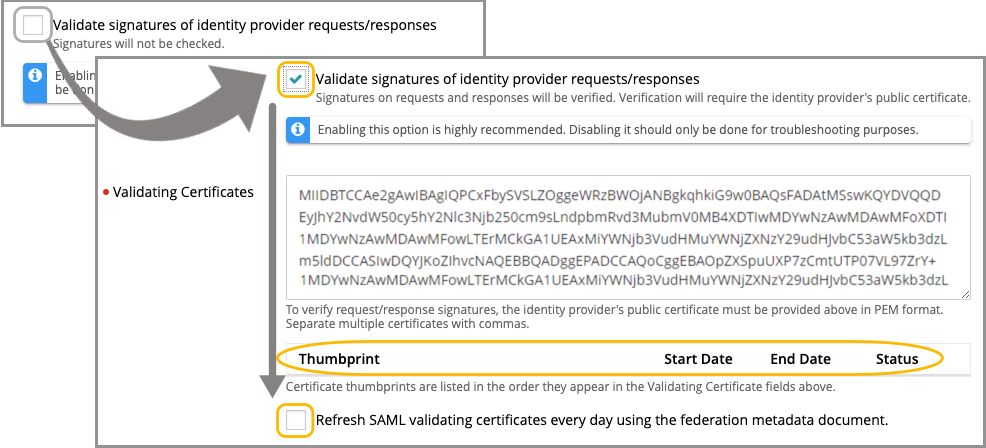
- Click Save Settings at the bottom of page.
- Ensure the Validate signatures of identity provider requests/responses check box is selected, then review the contents ot Validating Certificates field.
- In KACE Cloud, review and confirm the user attribute mappings.
At this point in the setup, user attribute mappings are pre-populated. They pre-populate consistently for Azure AD, Okta, and AuthO. However, some providers may use different names for common attributes. When using a different identity provider, confirm the naming conventions for common attributes and add manually.
.png)
- In KACE Cloud, assign user roles.
- In the Assign User Roles area, under Device User Role, select the applicable option.
The default setting is Automatic: Assign all SSO users the Device User role.
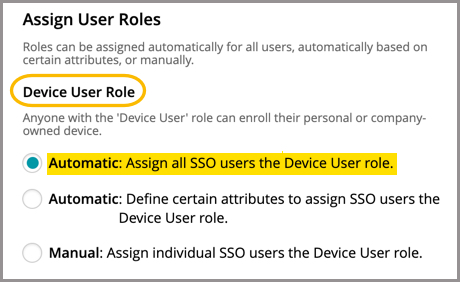
The setting can also be changed to either Automatic: Define certain attributes to assign SSO users the Device User role or Manual: Assign individual SSO users the Device User role.
If you select Automatic: Define certain attributes to assign SSO users the Device User role to assign the Device User Role to users belonging to a specific group, specify the attributes that you want to use to indicate which users are granted that role:
- Description: Specify a unique description for this group mapping.
- Attribute Name: Type http://schemas.xmlsoap.org/claims/Group.
- Attribute Value: Specify an attribute value from the http://schemas.xmlsoap.org/claims/Group node in the SAML document that corresponds to the group whose users you wish to automatically map to the Device Admin role.
- In the Assign User Roles area, under Device Admin Role, select the applicable option.
The default setting is Manual: Assign individual SSO users the Device Admin role. If you change it to Automatic: Define certain attributes to assign SSO users the Device User role, add the following values to the corresponding fields:
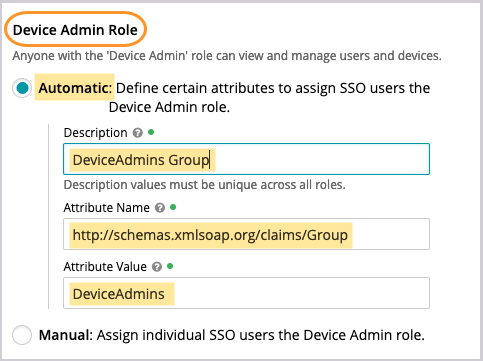
- Click Save Settings at bottom of page.
- In the Assign User Roles area, under Device User Role, select the applicable option.
- Obtain some additional details from Azure AD, then add them to KACE Cloud.
- In Azure AD, locate the Description value:
- Select Users and groups in the left panel of the main directory.
- Select All groups.
- Locate your group, then open to see details.
- Copy the Display name of the group.
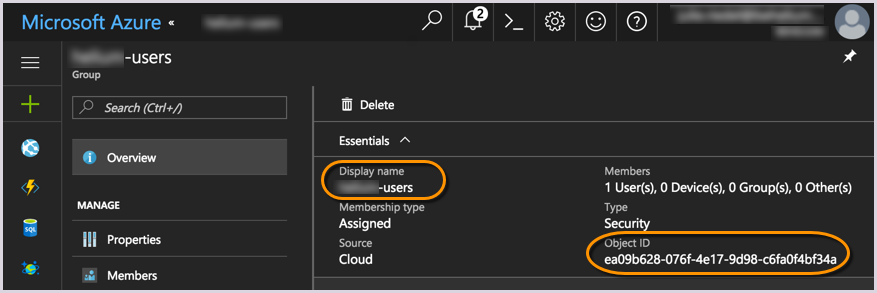
- In KACE Cloud, in the SSO Wizard, in the Description field, paste the newly copied group Display name from Azure AD.
- In KACE Cloud, in the SSO Wizard, in the Attribute Name field, type the following URL: http://schemas.microsoft.com/ws/2008/06/identity/claims/groups.
- In Azure AD, locate the Attribute Value value:
- Follow the same instructions used to locate the Description.
- Copy the Object ID of the group (see the above image).
- In KACE Cloud, in the SSO Wizard, in the Attribute Value field, paste the newly copied Object ID from Azure AD.
- In KACE Cloud, click Save Settings.
The locations and definitions for these values vary based on identity provider.
- In Azure AD, locate the Description value:
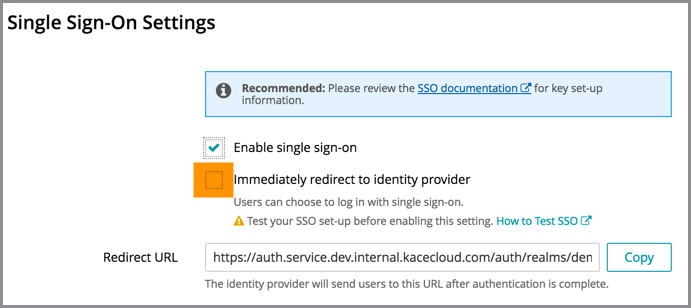
- In KACE Cloud, enable and test single sign-on.
- On the Single Sign-On Settings page, at the very top, select the Enable single sign-on (SSO) check box.
- Before selecting the Immediately redirect to identity provider check box, test the success of the single sign-on setup.
- Open a new incognito window or private browser to ensure login data is clear.
- Go to the KACE Cloud portal, but do not log in.
- Follow the Single Sign-On workflow using the customizable button.
In the example below, the Log in using your company credential button leads to the SSO workflow. The label on this button can be customized using the SSO Button Label field at the top of the SSO Wizard.
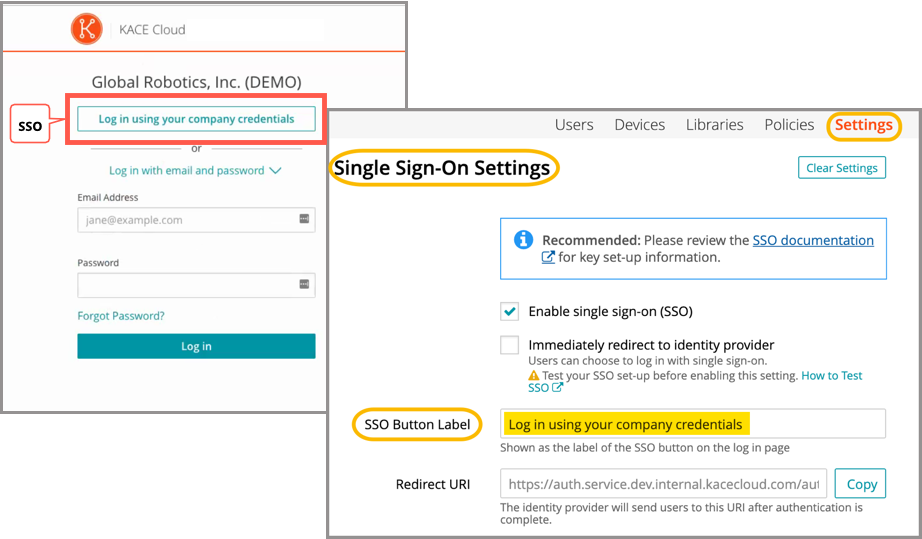
- On the KACE Cloud Microsoft login page login page that appears, log in using your identity provider credentials.
Single sign-on is successfully set up if the Users landing page appears in KACE Cloud:
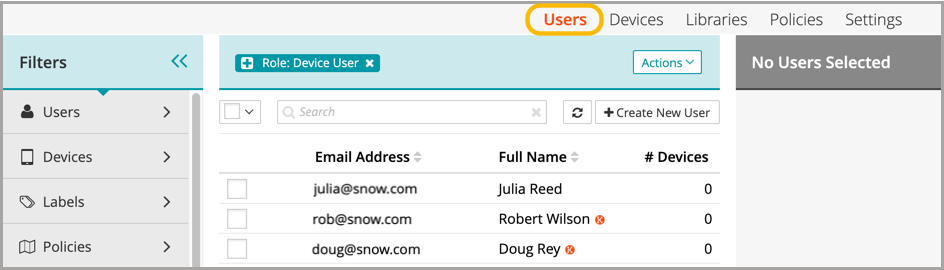
When the setup of single sign-on is successfully tested, users can be redirected to the identity provider's login screen.
Troubleshooting
| Problem | Solution |
|---|---|
| Single Sign-On button not visible on KACE Cloud portal. | Confirm that Enable single sign-on is checked on the SSO Settings page. |
| Error message on Microsoft login page: "AADSTS70001: Application with identifier ### was not found in the directory ###" |
Azure AD enterprise application Identifier (Entity ID) does not match KACE Cloud identifier. Revisit Step 1 and confirm that the Identifier (Entity ID) is copied correctly, and ensure that the end of the URL has been removed: /broker/heliumsso/endpoint. |
| Update password request on Microsoft login page. | If you have created a brand new Azure AD account, Azure will prompt you to reset your password the first time it is used. |
| Error message on Microsoft login page: "AADSTS50011: The reply address ### does not match the reply addresses configured for the application: ###" | Update the Azure AD enterprise application Reply URLs to include the reply address indicated in the error message. This property can be found in Azure AD under Enterprise application > KACE Cloud >Basic SAML Configuration > Reply URLs. |
| Error message on KACE Cloud portal. |
The identity provider successfully validated the username and password, but KACE Cloud did not accept the user. This may be because the user is not in the Azure AD group being assigned a device admin role. To troubleshoot:
|
| Single Sign-On misconfiguration or identity provider error |
As part of SSO, most companies will redirect their users to their identity provider's sign-in page. In the case of a misconfiguration or identity provider error, a device admin can bypass SSO by adding ?nosso=1 to the end of their product portal URL to turn off redirection and go directly to the KACE Cloud login screen. Example: https://yourcompany.kacecloud.com?nosso=1 |
| An "invalidFederatedIdentityActionMessage" error message is displayed on KACE Cloud portal. | The identity provider used a certificate to sign the SAML request/responses which does not match one of the certificates listed in the "Validating certificates" field of the KACE Cloud single sign-on configuration. Ensure that the list of Validating Certificates matches the list of certificates currently being used by your identity provider. Enable the Refresh SAML validating certificates every day using the federation metadata document field to have KACE Cloud automatically keep the Validating Certificates field up to date by attempting to retrieve the most current signing certificate information from the URL provided in the Federation metadata document URL field each day. |